Introduction
ESS Notifier is a notable security event scanner & notifier for Splunk Enterprise Security. The purpose of this tool is to send/push notifications via Email/Slack/REST API whenever a new security notable event is triggered on Splunk ESS.
This tool is ideally best used by Managed Security Service Providers (MSSP) who provide SOC as a Service.
Usage Scenarios
- Integration – Forward Security events to third-party systems via HTTP.
- Increase analyst vigilance by pushing security events to Slack channels & Email.
- Optimize analyst time by decreasing time spent on watching multiple Splunk dashboards.
Features
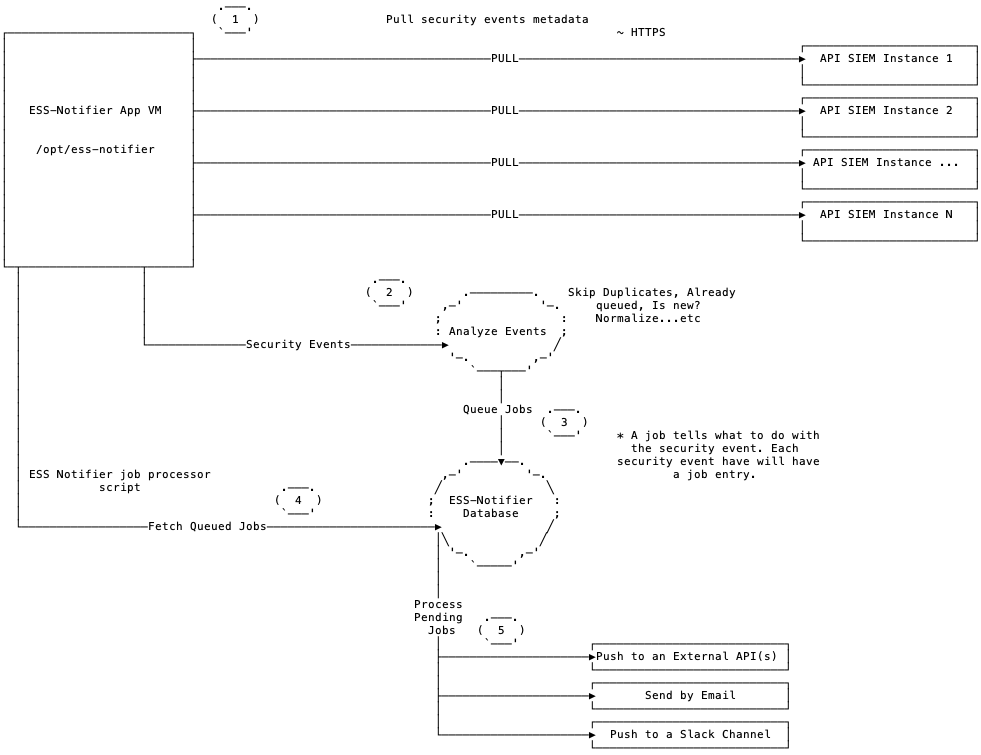
- Ability to connect & scan multiple Splunk Search Head instances.
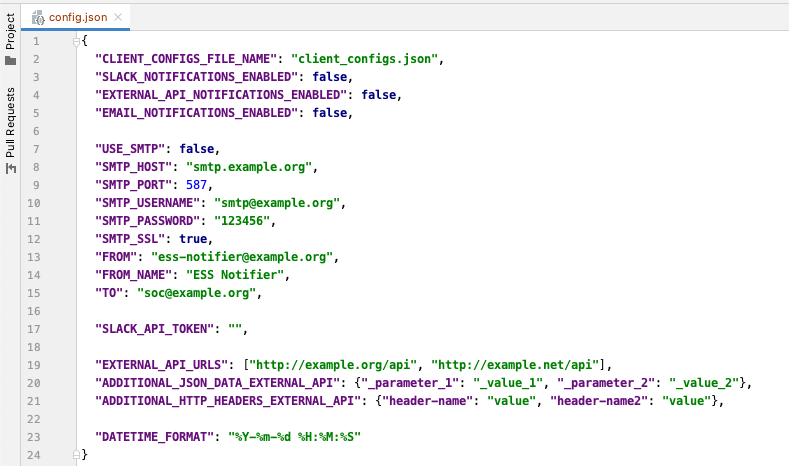
- Send notifications to multiple email addresses via specific SMTP server or SMTP Relay.
- Push notifications to multiple Slack channels.
- Integrate with other systems. Can forward Splunk notable events to external APIs via REST API.
- Custom external API payloads and HTTP headers.
- Customize notification templates in emsg_constructor.py
Prerequisites
- Network reachability to Splunk API port: TCP 8089 (HTTP/HTTPS).
- Internet access (in the case of Slack push notifications are enabled).
If you are managing multiple Splunk instances, then It’s recommended to set ESS Notifier on a dedicated server for increased security.
Installation & Usage
- Clone or download the project files
git clone https://github.com/iomoath/ess-notifier.git - install required libraries
pip install -r requirements.txt - Adjust your settings in
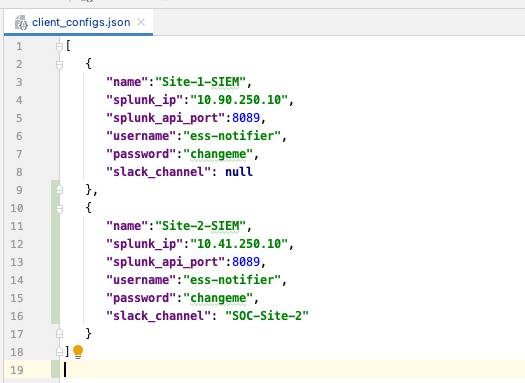
config.json - Add Splunk instance(s) information in
client_configs.json
To enable auto scan, enable cron service and create the following entries in crontab:
Create cron jobs to run every 1 minute. $ crontab -e and add the below lines
* * * * * /usr/bin/python3 /opt/ess-notifier/main.py -s &> /dev/null
* * * * * /usr/bin/python3 /opt/ess-notifier/main.py -e &> /dev/null
Usage
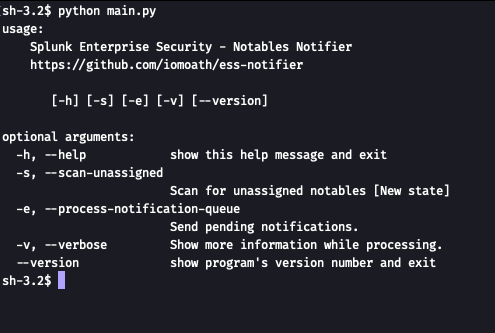
Scan for unassigned security notables:
python3 main.py -s
After the scan is complete, you can run the following command to send pending notifications if any:
python3 main.py -e
Sample Configuration files
Links
Project repository: https://github.com/iomoath/ess-notifier